SD-WAN is a cool feature to configure redundant internet access. But it was designed with load-balancing in mind and this brings some challenges to specific use cases. As an example, while you can use SD-WAN rules to define the preferred path for a specific application/system, it won’t prevent that the traffic is routed over another interface in case of an outage.
Imagine the following use case: You have a PBX system that only works over a specific ISP that is attached to WAN2. You’ve applied an SD-WAN rule so that all traffic from your PBX is routed to that particular interface.
Now if there is an interruption on that interface, the link monitor kicks in and disables any route involving that interface. The PBX now establishs a session over WAN1 (most likely your trunk won’t work anymore). But even if the WAN2 interface comes up again, the FortiGate won’t touch any active sessions and the PBX stays connected over WAN1.
There is a workaround (Routing Change and Session Fail-over with SD-WAN) regarding that situation, but it will change the behaviour of the firewall at the global level.
FortiOS 6.2
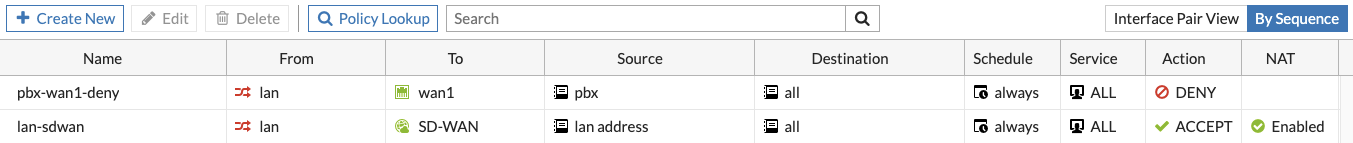
Since FortiOS 6.2 you have a better option: Even if your WAN interfaces are members of the SD-WAN, you can configure individual firewall policies for them. That allows you to configure a deny policy for your PBX involving the interface WAN1. Just remember to put it on top of the firewall policies using the sequence view:
FortiOS 6.4
FortiOS 6.4.1 introduced a new concept called SD-WAN zones. By design you cannot use interfaces assigned to a zone in individual policies. But you still have the option to create a seperate SD-WAN zone for each WAN interface. Then you’ll either have to create redundant firewall policies or enable the “Multiple Interface Policies” feature (you’ll lose the Interface Pair View).
FortiOS 7.0 / 7.2 (Updated 19.12.2023)
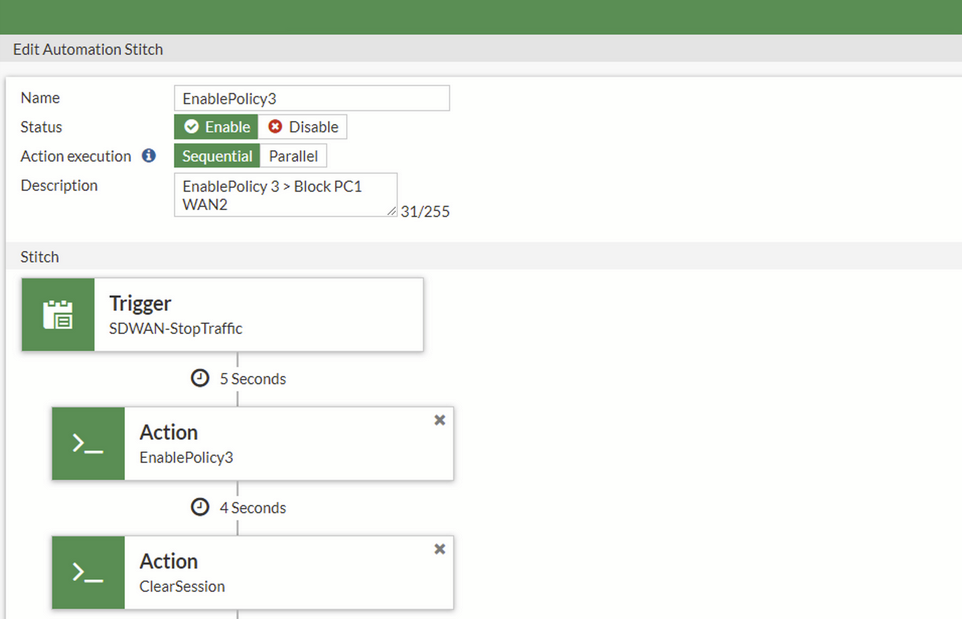
With the Automation Stitches, a new variant has been added to automatically activate a firewall policy if an interface has failed. This allows you to activate a deny policy if a specific interface has failed:
https://community.fortinet.com/t5/FortiGate/Technical-Tip-Deny-traffic-to-a-WAN-interface-on-an-SD-WAN/ta-p/266317
![]()

