Last Update: 12.03.2026
Some providers (like init7.ch which already uses the Swisscom XGS-PON) do encapsulate their PPPoE traffic into a VLAN Tag (802.1Q or Q-Tagged). The reason for this is, that in the majority of the cases the provider is using a layer 2 network (last mile) of another provider, which uses VLAN tagging to differentiate the traffic to different service providers.
The configuration of the FortiGate is not too complicated in those cases. It is even possible to make the whole configuration directly off the WebGUI.
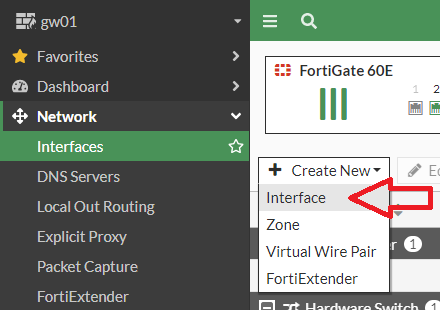
- Navigate to “Network” and then to the “Interfaces” page on the WebGUI of your FortiGate.
- Create a new Interface:
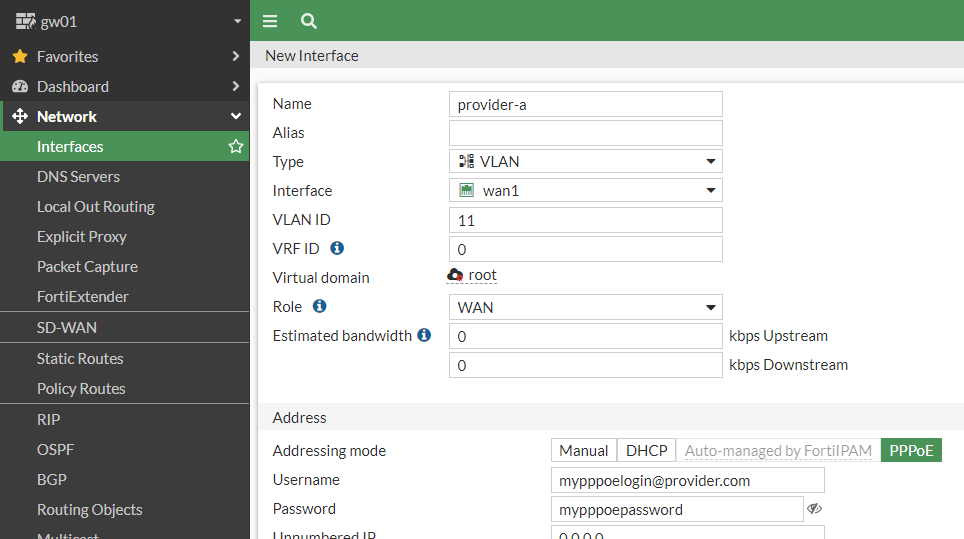
- Change the Type of the Interface to “VLAN” and set a name for the interface.
- Choose the physical port where the VLAN is terminated.
- Enter the VLAN ID and set the ID which your provider tells you.
- Set the PPPoE Login and save the configuration.
Wait a minute or two until the PPPoE connection is shown as “up”.
If you like to configure it on the CLI, you may use this block as a template:
config system interface
edit "provider-a"
set mode pppoe
set role wan
set username "mypppoelogin@provider.com"
set password mypppoepassword
set interface "wan1"
set vlanid 11
next
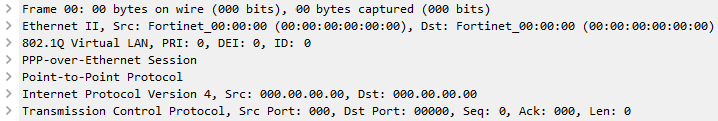
endFor all that are interested in a wireshark trace, here we made one for you. You can see clearly, that the PPPoE is placed inside the VLAN Tag:
And we have even one more secret for you: Any traffic passing a PPPoE interface (including VPN tunnels) can not be hardware accelerated by neither of the security processor chipsets (We also have more details regarding this topic here). Please keep this detail in mind when you think about the sizing of a PPPoE based setup.
– PPPoE topic closed –
In Switzerland, usually you have to decide if you want to use DHCP or PPPoE for DSL connections. DHCP has a bit less overhead (because the PPP header is not needed), but you can not set static IP addresses over DHCP (that is when PPP is necessary).
If you decide to use DHCP, the following information may be interesting for you:
The last important information that may be of interest for you is the following: The FortiGate is supporting the use of DHCP client options since FortiOS 6.4. Therefore it is now possible to set the DHCP client option number 60, which is the vendor class identifier (short: VCI).
On the Swisscom information page for the “configuration of third-party routers” you can find all the settings you need to set for a swisscom DSL and FTTH line. In the Fortinet new feature guide for FortiOS 6.4 is a guide how to configure the DHCP client option.
In the case that you are using a bridge or the Fortinet own SFP DSL transceiver (SKU: FN-TRAN-DSL), the configuration on the WAN interface looks like following:
config system interface
edit "wan1"
set mode dhcp
config client-options
edit 60
set code 60
set type string
set value "100008,0001"
next
end
next
endSome people found out, that you can prevent a re-registration of the internet connection if you set the MAC address of your old modem on the FortiGate WAN interface like following:
config system interface
edit "wan1"
set macaddr 00:11:22:33:44:55
next
endIn PPP passthrough mode, Swissom now also supports a higher MTU on the underlaying interface. This allows to send PPP packets with an MTU of 1500, so no fragmentation is needed anymore! Since the PPP header is 8bytes long, the MTU on the WAN interface has to be configured to 1508. This is documented under https://cb-guide.swisscom.ch/diverses/all_about_mtu/ .
![]()


Hi boll.ch,
thank you for the hint that no hardware acceleration is available with PPPoE – I totally missed this reading the official docs.
What options do I have left then, if my ISP supports only PPPoE?
In Germany, the major ISP Telekom provides us with classic VDSL2 and a single static /32 IP – and PPPoE.
As far as I can see, my only options are:
– use a modem like DrayTek Vigor165, deal with PPPoE on my FortiGate and loose hardware acceleration
– replace the modem with a router, which handles the PPPoE part, point the FortiGate to the router gateway, but deal with double NAT
Is there any other way to let another device handle the PPPoE part without introducing double NAT inside my network?
Greetings
Denis
Hello Denis
Thanks for your feedback.
As you correctly understood, you will lose the hardware acceleration as soon as you use PPPoE on your Fortigate. If you don’t want to lose the hardware acceleration, your second idea goes certainly in the right direction. When using a router in front of the Fortigate that is configured with PPPoE, you can use the Fortigate behind the router in two modes:
– Transparent mode
– Routing mode without NAT
In both above cases the hardware acceleration will work, since Ethernet encapsulation is used.
Kind regards
Boll Engineering Tech Team